What can we learn from recent gaming sector security incidents?
MGM Resorts International suffered a major cybersecurity breach that affected everything from electronic hotel room keys to the operations of its casinos and websites. The impacts, which have lasted more than a week as of this writing, are costing the company between an estimated $4.2 million and $8.4 million a day.
And that’s not all. Caesar’s Entertainment, Inc. admitted that it had been victimized recently in the same way, but had paid millions of dollars to the perpetrators to avoid the same kind of shut-downs, outages and damage that befell MGM.
How could such large, well-resourced and security conscious companies fall victim to such damaging attacks and what can the rest of the corporate world learn from it?
Unfortunately, you can’t completely defend yourself from this kind of breach, especially since cyber criminals are inventing new weapons all the time. But, with the help of thorough research and risk-management tools, you can work to beat the odds.
Cyber risk is increasingly predictable and quantifiable, and given the impacts on business operations, reputation, regulatory compliance, and share price, institutional investors are leveraging cyber risk quantification tools in making their investment choices. At the very least, they are using these tools to drive more informed conversations with subject companies to ensure that they have a shared view of risk.
What happened?
First reported on Sept. 11, MGM indicated that a “cybersecurity issue” was impacting some of its systems, and that the company was shutting down certain networks and services to protect the company and its customers. Websites went down, digital room keys were disabled, and slot machines were not working. Casinos went into “manual mode,” issuing written receipts for winnings in order to stay semi-operational.
Empty casino floors and long lines of guests trying to access to their rooms made for somewhat shocking footage on the evening news, ensuring that this well-known brand would be in the headlines for more than a moment. While there is undoubtedly more to learn about the origins of this incident, a consensus has formed around the basics of the attack. A group known as “Scattered Spider” is currently believed to have originated the problem at MGM through a “vishing” attack (gaining system access through impersonating an employee on a telephone call). Once the credentials were in their hands, a ransomware-as-a-service known as BlackCat was unleashed in MGM’s systems.
Shares of MGM Resorts lost roughly $850 million in market value between the day the incident was first reported and Sept. 19.
No one is completely safe
Any organization can fall victim to a cyber breach incident, especially when they are up against a determined bad actor. Networks are complicated and tied to an endless maze of physical and virtual systems, as well as to third-party suppliers and business partners. Even well-run firms with impeccable security can be breached – falling victim to a new zero-day vulnerability, a concerted and well-planned attack, a partner’s lapse in diligence, or by simply making a small but exploitable mistake.
Some companies simply need to do a better job playing their hand – understanding their background risks (which vary widely by sector and industry) as well as their specific situation with respect to the exposure of their network assets, the skill sets of their team members, and the vulnerabilities of their systems.
Most firms fall into the grey area in between. They do some things well, and others not so well. They have risks that are inherent to the sector they serve, but have deployed mitigating systems and controls. Some business units perform well, while others are challenged. They have people who are highly skilled in managing network security, but other employees that are less educated and less focused on cyber risk. They have areas of excellence and areas of weakness and usually an incomplete understanding of both. Maximizing your chances of staying safe requires that you constantly monitor for risk, discover your own weaknesses, and keep track of the odds.
Gaming sector performance
Leveraging the ISS ESG Cyber Risk Score, ISS Corporate Solutions compared the cyber security risk of the gaming sector against the broader market. Specifically, we looked at the cyber score performance of 20 gaming firms and compared key risk metrics for these firms to the same metrics for the Russell 3000 companies. The ISS ESG Cyber Risk Score is a forward-looking (predictive) metric corresponding to the likelihood (incident odds) of a future material breach event. It is generated by assessing how well a company manages and maintains its network security. It evaluates the condition and exposure of internet-exposed assets (networks and websites), gathers evidence of compromise, and assesses consistency and skill in configuration and management of systems through key metrics that are correlated with breach outcomes. The score is powered by a machine learning model trained on real breach exemplars to understand the mathematical relationship between risk signals and breach outcomes.
Anecdotally, casinos and other gaming firms are considered to be higher risk and a rich target for hackers. The data bears this out.
Gaming Sector vs Russell 3000
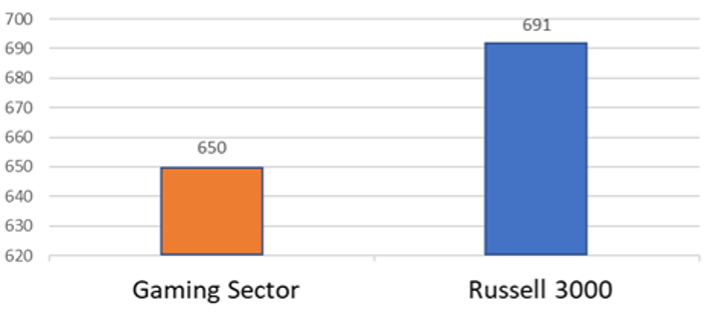
Source: ISS ESG; data as of September 18, 2023
The score is engineered to correspond to incident odds; specifically the odds of a material breach event occurring in the next 12 months. The 41-point difference measured here corresponds to a 30% difference in incident odds between the groups – i.e. gaming sector companies, on average, are 30% more likely to incur a significant breach event in the next 12 months that the broader market represented by the Russell 3000 companies.
The ISS ESG Cyber Risk Score is also packaged with other explanatory metrics and contextual tools to aid the user in decision making. One of these tools is the Incident Type Likelihood (ITL) score, which describes the type of incident most likely to occur should the company become a victim of a material cyber incident. The most likely incident type for nearly all sectors is “Third Party” breach; but the second and third most likely type for the gaming sector are “Ransomware/Malware” and “Social Engineering/Phishing” – closely aligned with the recent attacks on MGM and Caesars. About 95% of the gaming companies analyzed have this combination of risks, while it’s only 60% for companies generally. Learn more about sector-specific Incident Type Likelihood here.
To win with investors as well as customers, companies should look at themselves through the same lens as those who are watching them. Mitigating risk starts with identification and understanding. This includes sector-level risk as well as risks that are unique and specific to a firm. Companies and their CISOs are rightly focused on the risks they know about; but sometimes it can be helpful to see yourself from the point of view of other key stakeholders. Identifying risks that may be out of your normal field of vision can be insightful, and may well keep a company out of the headlines.
Better measurements yield better management
ISS Corporate Solutions can support your company with key cyber risk assessment and identification capabilities (both for your company and you supply chain) by utilizing the ISS ESG Cyber Risk Score – a concise, empirical, and forward-looking metric that determines the likelihood of a future breach event by assessing how well a company manages and maintains its network security. It is powered by a machine-learning model trained on real breach exemplars to understand the mathematical relationship between risk signals and breach outcomes. It is packaged with insightful contextual tools that help companies understand and address cyber risk, including third and fourth-party exposures. Contact us to learn how ISS Corporate Solutions can help you best navigate these new requirements.
Authored by:
Douglas Clare, Managing Director, Cyber Strategy, ISS Corporate Solutions